Cybersecurity expert explains how 4 million payment cards appeared on the dark web
Researchers estimate that an average payment card can be cracked in just six seconds. A study released by NordVPN analyzing 4 million payment cards from 140 countries finds that the most common method to hack a payment card is brute forcing. This type of attack is incredibly quick and can be executed in a matter of seconds.
“The only way such a huge number of payment cards could appear on the dark web is through brute forcing. That means that criminals basically try to guess the card number and CVV. The first 6-8 numbers are the card issuer’s ID number. That leaves hackers with 7-9 numbers to guess because the 16th digit is a checksum and is used only to determine whether any mistakes were made when entering the number. Using a computer, an attack like this can take only six seconds,” Marijus Briedis, CTO (chief technology officer) at NordVPN, says.
How do brute-force attacks work?
In a brute-force attack, a hacker uses a rapid trial-and-error approach to guess the correct password, PIN, or in this case payment card number. It doesn’t require a lot of brainpower or complex algorithms – it’s merely a guessing game. However, the attack does require some resources – time, computing power, and a special type of software used by criminals.
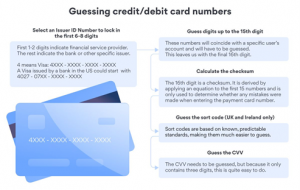
“To guess the nine digits that are needed to have a full card number, a computer has to go through 1 billion combinations. And it will only take one minute for a typical computer, which can try around 25 billion combinations per hour. However, depending on the card issuer, a criminal may need only seven digits to make a correct guess. In this case, six seconds would be enough,” says Marijus Briedis.
Most card issuers limit the number of guesses you can make in a short space of time to prevent these kinds of attacks, but criminals find ways to get around the limitations. Mastercard, for example, has a centralized authentication system. So a criminal can only try around 10 times with one number before Mastercard’s centralized system detects that. With the Visa security system, a criminal can try 30 to 40 times, maybe even more. And if they pick the right time of day, when it’s really busy, they can try many more times because it has a decentralized federated system.
This correlates with the fact that more than a half (2,524,142) of all the discovered payment cards were Visa, followed by Mastercard (1,602,248) and American Express (215,971).
Can you do anything to protect yourself?
There is little users can do to protect themselves from this threat, short of abstaining from card use entirely. The most important thing is to stay vigilant.
“Review your monthly statement for suspicious activity and respond quickly and seriously to any notifications from your bank that your card may have been used in an unauthorized manner. Another recommendation is to have a separate bank account for different purposes and only keep small amounts of money in the one your payment cards are connected to. Some banks also offer temporary virtual cards you can use if you don’t feel safe while shopping online,” Marijus Briedis says.